The paper introduces the case study for attack surface analysis and monitoring with practical application of open-source intelligence (OSINT) methods. The case is based on the perimeters of healthcare organizations and aims to introduce the threat landscape of healthcare industry as well as methods to collect information about entry points and assets on network perimeter. Techniques and tools in this paper are not limited by organization type and can be applied for different network assets to prepare initial information during first stage of penetration testing and red team operations.
red teaming
Красная команда имитирует действия атакующего, чтобы помочь оценить эффективность защитных мер и улучшить безопасность. В этой статье я разберу, как устроены такие команды и какие нужны области экспертизы для успешной реализации kill chain и демонстрации результатов.
В прошлый раз мы познакомились с ключевыми целями и показателями эффективности Red Team для процессов ИБ и бизнеса в целом. Мы рассмотрели особенности взаимодействия экспертов наступательной безопасности c Blue Team, нюансы ведения проектов и коммуникации во время работ. При этом мы практически не коснулись внутренней структуры красной команды. Пора исправить это!
Индустрия информационной безопасности асимметрична: атакующий находится в более удобном положении, чем специалист по защите. Атакованной стороне нужно быть эффективной всегда, 24/7, а нападающей достаточно быть эффективной лишь единожды. Кроме того, у атакующего есть возможность тщательно изучить свою жертву перед активной фазой атаки, в то время как другая сторона начинает изучение нарушителя уже во время этой атаки.
В одной из прошлых колонок я рассказал о стадиях целенаправленных атак (kill chain). Первая стадия, стадия «разведки», начинается задолго до того, как атакующий дотронется до первой машины жертвы. От количества и качества данных, собранных на этом этапе, зависит успешность атаки и, самое главное, стоимость ее проведения.
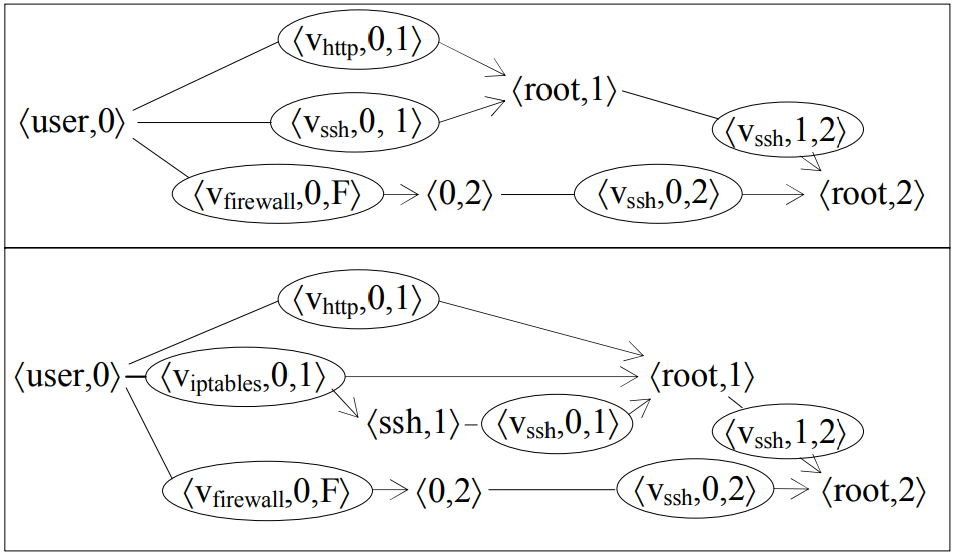
During the previous post, we discussed the meaning of the different types of attacks, which are extremely complex and involve a large number of targeted actions performed by attackers. In this part, I would like to talk about so-called quantitative research of the attacks used to analyze the maturity level of existing protective technologies and security approaches.