Индустрия AppSec десятилетиями жила в жёстком конфликте между полнотой и точностью поиска угроз. Классические SAST‑инструменты генерируют шум, на ручной разбор которого уходит больше времени, чем на реальную работу с угрозами. Релиз Claude Code Security от Anthropic заметно встряхнул индустрию кибербезопасности: капитализация традиционных вендоров просела, а генеральный директор крупного игрока Snyk заявил, что будущее компании теперь должен определять ИИ‑центричный лидер.
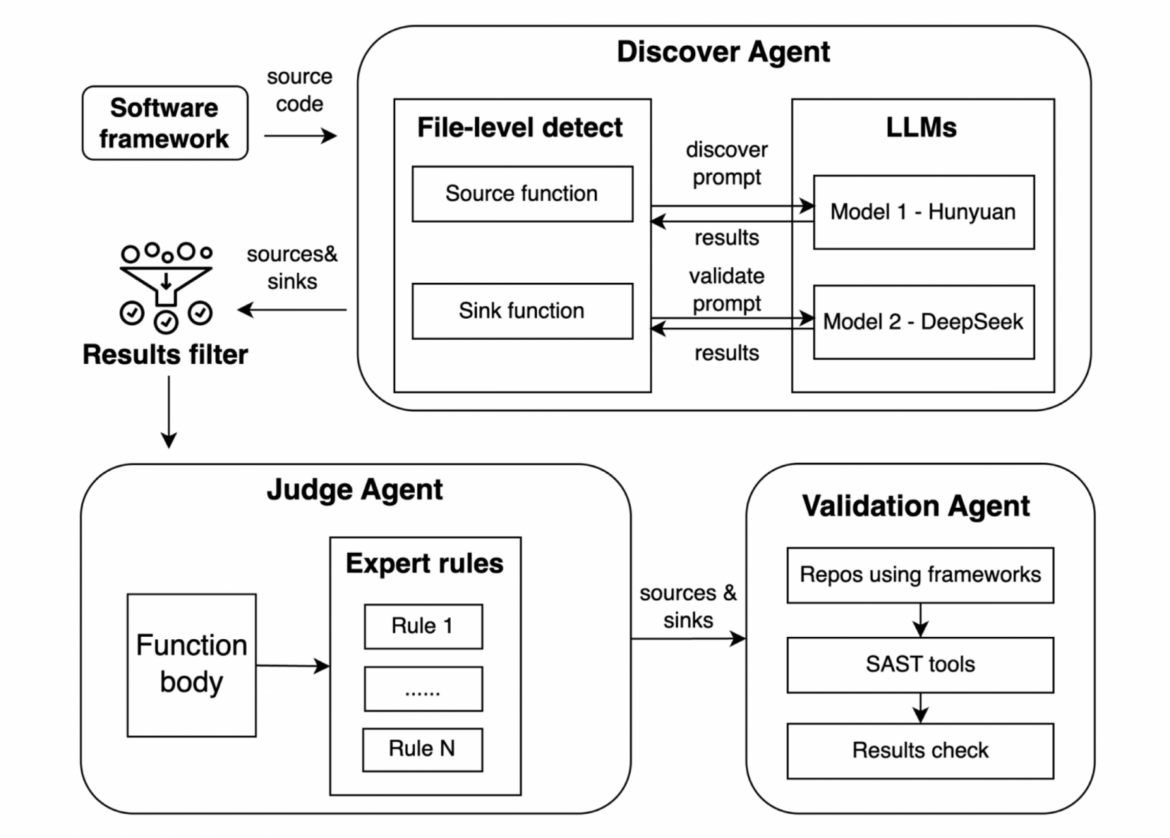
Рынок переопределил ценность инструмента безопасности. Раньше она измерялась количеством поддерживаемых правил и языков. Сегодня формула изменилась: важна цепочка “нашёл, объяснил, помог исправить”. Здесь на сцену выходят LLM — не как замена классическому анализатору, а как дополнительный слой интерпретации. Так формируется новая категория — AI SAST.
В этой статье разберём, как именно LLM работают с кодом, почему «скормить репозиторий в промт» — плохая идея, какие инженерные метрики действительно важны и как мы исследуем и внедряем новые возможности автономного поиска и исправления дефектов в коде для добавления в продукты SourceCraft Security.