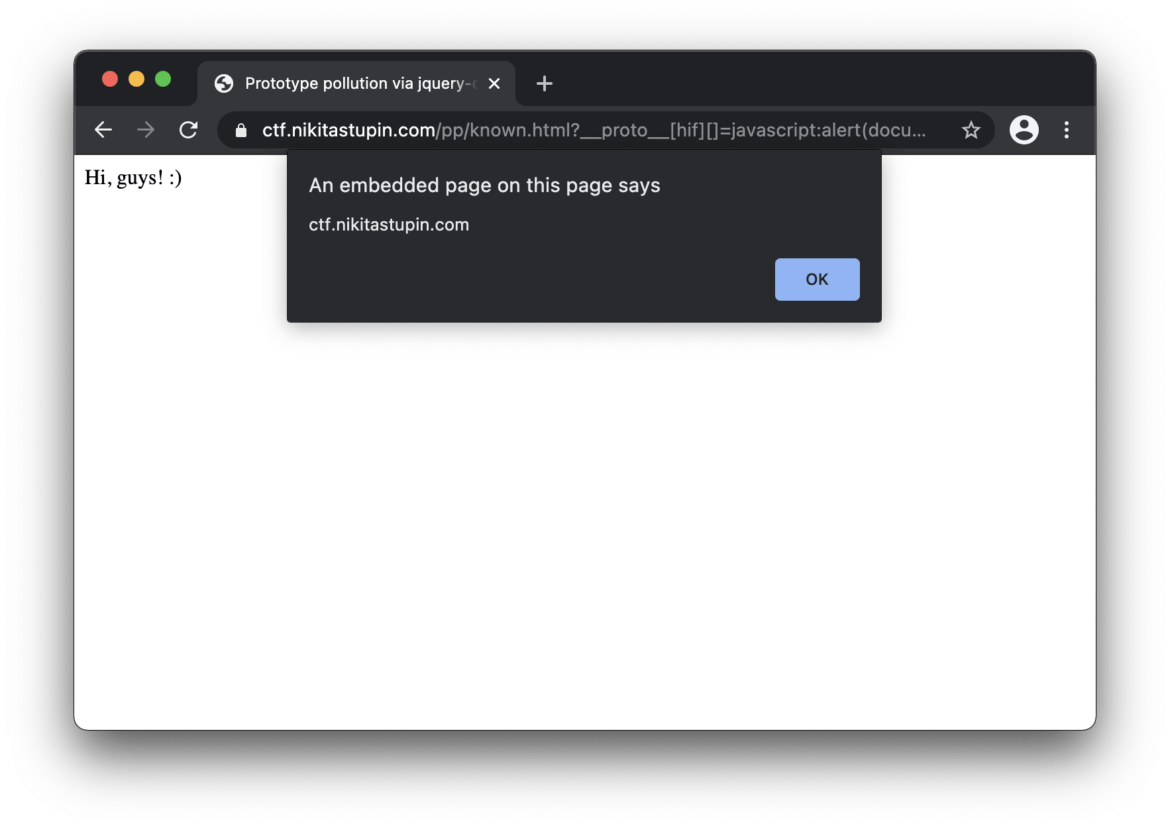
If you regularly monitor bug bounty reports, you’ve seen “JavaScript prototype pollution” titles. Nikita Stupin decided to dig deeper into the category of vulnerabilities, impacting JavaScript applications, and prepared the practical guide of its discovery and exploitation. Soon we will also prepare an English version of the paper, but currently, you have to manage by yourself to translate it.
sdlc
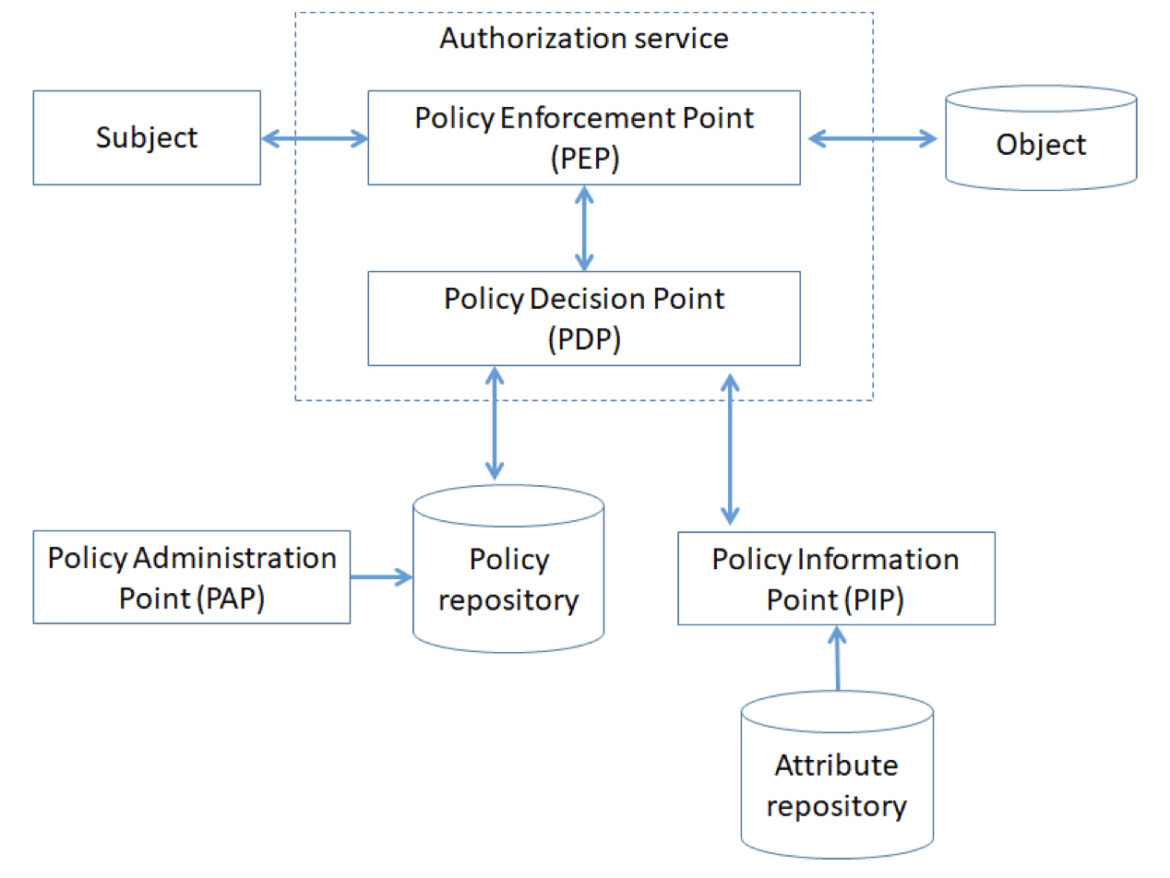
Authentication, Authorization, and Audit (AAA) in microservice-based architecture is a cornerstone for any scale applications. Multiple “best practices” by technology leaders, multiple recommendations by industry influencers. What is relevant to your product design and should be implemented?
We published the survey deliver the AAAnswers with the criteria for choosing the right one for your application security architecture: “Authentication and authorization in microservice-based systems: survey of architecture patterns.”
Objective: the aim of this study is to provide a helpful resource to application security architect and developers on existing architecture patterns to implement authentication and authorization in microservices-based systems.
You know that product security strategy, if properly integrated into DevOps process, can improve the product. But do you know, how product security can destroy the product?
Join my talk on Security Stage at the upcoming @infosharepl 2020 Online, where I will speak about “Dev, Sec, Oops” principles.
Let’s meet on 23-25 and 28-30 September 2020. Book a ticket using promo code “is20-dmakrushin” to get 10% off. Register: https://infoshare.pl/is-register/
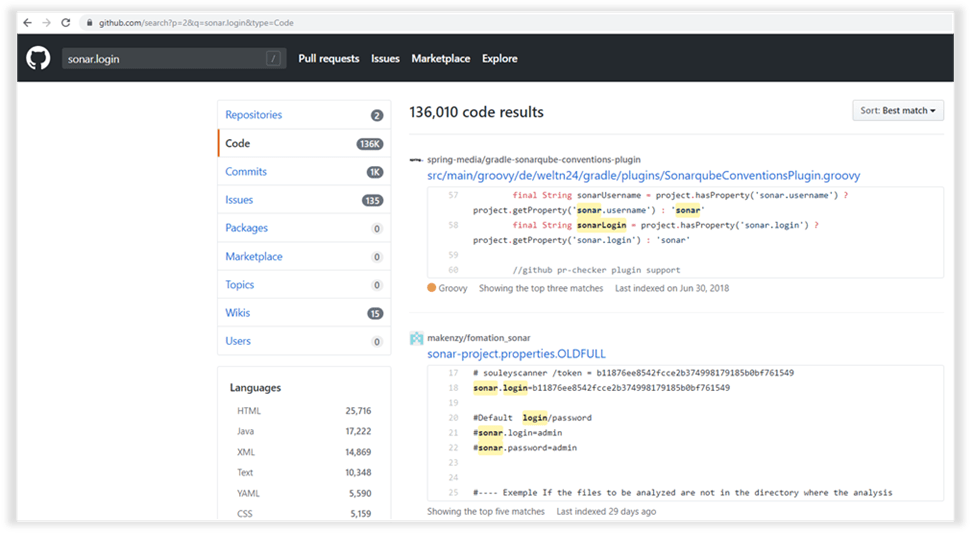
При разработке софтверного продукта или облачного SaaS-сервиса достаточно трудно отслеживать сторонние активности всех специалистов, вовлеченных в процесс разработки. Достаточно открыть Github, ввести в поиске «<имя_домена_компании.com> pass» и оценить выдачу. В том случае, если вдруг Github действительно показывает в своей выдаче что-то интересное, то мы рассмотрим сценарии, которые могут помочь злоумышленникам нарушить бизнес-процесс твоей компании. А если Github все же молчит, то рассмотрим альтернативные варианты атаки на цикл разработки продукта, при которых точкой входа в инфраструктуру могут стать не только разработчики, но даже Security-инженеры.